Blog
In an era where artificial intelligence (AI) is rapidly evolving and permeating various aspects of business operations, the need for an AI Acceptable Use Policy (AUP) has become increasingly apparent. As companies...
It’s that time of year again for the National Cyber Security Alliance’s (NCSA) Data Privacy Week. This year Data Privacy Week is January 21 – 27th 2024. Data Privacy Week is an...

Microsoft has recently begun a campaign to require use of the Microsoft Authenticator app for multi-factor (MFA) authentication to Microsoft 365 accounts. This means that SMS and voice-based MFA authentication, which are...

October is here, and with it comes Cybersecurity Awareness Month, a time to focus on safeguarding our digital lives. This is the 20th year of the Cyber Security Awareness Month campaign and...

LinkedIn is undoubtedly one of the most popular platforms for professionals, job seekers, and businesses. With over 774 million users worldwide, it’s a treasure trove of career opportunities, networking, and industry insights....

The list of popular companies that many of us interact with or use for services that have had breaches continues to grow in 2023. With cyberattacks becoming more sophisticated, knowing how to...

In today’s rapidly evolving digital landscape, businesses face increasing challenges in securing their systems and data. As technology advances, so do the tactics employed by cybercriminals. One powerful tool to combat these...

Social engineering attacks remain one of the top cybersecurity threats to companies in 2023. According to recent research, businesses experience an average of over 700 social engineering attacks annually, and these attacks...

As we become more and more reliant on technology, the security of our computers and digital devices has become increasingly important. Cybercriminals are constantly looking for ways to infiltrate digital systems and...
As we all continue to navigate an ever-expanding digital landscape, we must be aware of the trail of data we leave behind. This year, during Data Privacy Week, which is taking place...
In 2022, there were 15 million data breaches worldwide in the third quarter of the year alone, meaning the risk of cyberattacks remains high. As the end of the year approaches, it...

In 2004, October was declared Cybersecurity Awareness Month. Dedicating October to cybersecurity helps raise awareness about the importance of protecting our personal and professional information. As we see this focus on cybersecurity...

What is ZuoRAT and how does it work? Remote Access Trojans (RAT’s) have existed since the 1990’s. They are malicious software designed to remotely control an infected computer, while remaining undetectable. What...

Cyber threats and attacks are rising, costing companies money and time. According to the FBI, in 2021 alone, companies lost around $6.9 billion. So how can organizations protect themselves? In this post, we’ll...

Microsoft recently launched the New Commerce Experience (NCE). The goal was to give customers greater choice and flexibility in how they purchased their Microsoft product licenses. There are changes in the billing...

Since the onset of the COVID-19 pandemic, consumers and producers have learned to adapt to many new and unforeseen challenges and hardships. For biotech companies in 2022, navigating the shortages and delays...

Companies across all industries are dealing with supply chain issues and shortages in 2022. From extended delivery times to product unavailability continuing for weeks and months, companies have had to learn to...

With the threats that businesses face today, you may be considering cyber and ransomware insurance. Many insurance companies are even starting to include questions related to cyber and ransomware for typical errors...
In 2022, Data Privacy Week is taking place from January 24-28. It is crucial to raise awareness about data privacy during this week-long initiative. However, data privacy concepts remain essential for securing and managing...

Life science companies have unique IT needs at every stage. It can be challenging to judge whether it is a better use of your resources to establish an internal IT team or...

Your biotech startup has an endless list of things to keep in mind as you build out your company and pursue your essential work. It is critical to stay away from potential...

October has been dedicated to Cybersecurity Awareness Month every year since 2004. However, as this year’s Cybersecurity Awareness Month comes to an end, your Data Evolution experts are here to remind you...

Your network infrastructure takes time and effort to strategize and develop. Any compromise to your network or infrastructure can disrupt connectivity, communication, and other operational activities. Network infrastructure security is crucial to...

Password hacking happens every day, and not just to large corporations or governmental organizations. Cybercriminals can profit so much from hacking any person’s accounts that it is well worth the effort for...
When was the last time you changed your personal password? Do any of your accounts share passwords, or have you shared your password with someone else? Regularly changing your passwords is a...
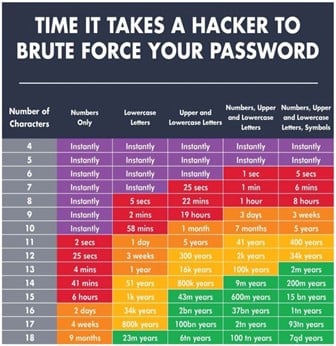
Your passwords are like the lock to your house. You would not offer the keys to random people or install a simple lock that any criminal could pick easily. Any compromise to...

Network devices such as laptops, tablets, or servers make it easier than ever for organizations to collaborate and accomplish work together. However, these devices, also called endpoints, also provide many potential entry...

These days, social engineering attacks are one of the top threats to your company’s cybersecurity. A recent study found that, on average, organizations get targeted by more than 700 social engineering attacks per...

Taking email security measures seriously is more critical than ever. Phishing emails come in many forms and present severe threats to your company’s intellectual property, daily workflows, and finances. Successful cybercriminal attacks...

Cloud services offer flexibility, security, and convenience to life science companies. In such a fast-paced and competitive industry, these benefits are not to be taken lightly. Whether you need to handle complex...

If you read or watch the news, then it is no surprise that companies’ electronic systems get compromised all the time, whether big or small. The biotech and life science industry is...
Biotech and life science companies tend to grow quickly. Your team may grow from two to thirty or more in a single year, and your workflow needs to scale and pivot smoothly...
Life science companies regularly deal with intellectual property and expensive lab equipment, making them an appealing target for cybercriminals. This is a major issue on two crucial fronts: Cybersecurity threats can disrupt...

A data breach has the potential to cause reputation damage, financial ramifications, and legal liability. Any company with sensitive data or intellectual property must ensure their work is secure. Data security is...

IT disasters can range from a minor inconvenience to a dilemma that brings your work to a screeching halt, and they are more common than you might think. Things can go wrong...
Search
Tags